Introduction
For decades, enterprise security has revolved around a single concept which is "Protect the credentials".
From passwords to API keys, tokens, and certificates - organizations have invested heavily in tools designed to store, rotate, mask, and monitor credentials.
As a result, Privileged Access Management (PAM) emerged as the industry standard to control and secure privileged accounts.
Then came 'Zero Trust' - promising a more dynamic and secure model.
Yet today, breaches continue to increase - and the root cause remains the same:
Credentials are still being stolen, reused, and abused.
The Real Problem - Credentials Should Not Exist
Modern attackers don’t break systems. They leverage valid access.
Phishing steals credentials
Malware extracts tokens from memory
Sessions are hijacked and replayed
Insider threats misuse legitimate access
Even the most advanced security stack fails when:
Access is granted through something that can be copied, stolen, or replayed and reused.
This is the fundamental flaw:
Security has been focused on managing credentials instead of eliminating them
Why PAM Is No Longer Sufficient
Privileged Access Management (PAM) was designed to reduce risk but not eliminate it.
PAM Improves Control - But Keeps the Core Risk Alive
PAM solutions:
Store credentials in vaults
Rotate passwords
Broker access through jump servers
Record sessions ( even not low-level )
But at runtime:
Credentials are still retrieved and used
And that is exactly where attackers operate.
1. Credentials Still Exist in Memory and Sessions
Even with vaulting:
Credentials are exposed at the moment of use
Tokens and secrets live in application memory
Sessions can be captured or replayed
Attackers no longer target storage - they target:
Execution time
2. PAM Detects - But Does Not Prevent
PAM excels at:
Session recording
Activity monitoring
Audit logging
But:
Detection happens after access is already granted
In modern attacks, this is too late.
3. PAM Is Not Context-Aware
Most PAM implementations:
Do not evaluate device security posture
Do not consider behavioral anomalies
Do not dynamically adjust trust
This means:
A valid credential can grant access from an untrusted device or compromised environment
4. PAM Introduces Complexity Without Eliminating Risk
Organizations end up managing Vaults, Jump hosts, Proxy layers and Rotation engines
This leads to:
More infrastructure - but the same underlying vulnerability
The Problem with “Modern” Zero Trust Implementations
Zero Trust is the right concept - but many implementations fall short.
They Still Rely on Credentials
Tokens replace passwords
Certificates replace secrets
But:
They are still credentials - just in a different form
They Are Often SaaS-Based
Many platforms:
Route traffic through vendor-controlled infrastructure
Store identity and access data externally
Depend on cloud-managed control planes
For organizations in:
Saudi Arabia
United Arab Emirates
Bahrain
GCC …
This creates serious concerns around:
Data sovereignty
Regulatory compliance (SAMA, NCA, PDPL, UAE IA)
Full control over access and audit data
They Lack Deep Context Awareness
Most solutions stop at Identity verification as being only Identity-aware maintained.
But ignore:
Device trust
Runtime behavior
Continuous validation
They Remain Fragmented
Organizations still need:
PAM
EDR
DLP
IAM
Zero Trust becomes an addition - not a transformation
Secureify Trust: A Different Approach
Secureify Trust was designed to solve the root problem:
Eliminate credentials entirely - not manage them
1. True Credential-less Access
Secureify Trust removes:
Passwords
Shared secrets
Retrievable credentials
Access is:
Dynamically generated
Policy-driven
Ephemeral
Nothing exists that can be:
Stored
Stolen
Reused
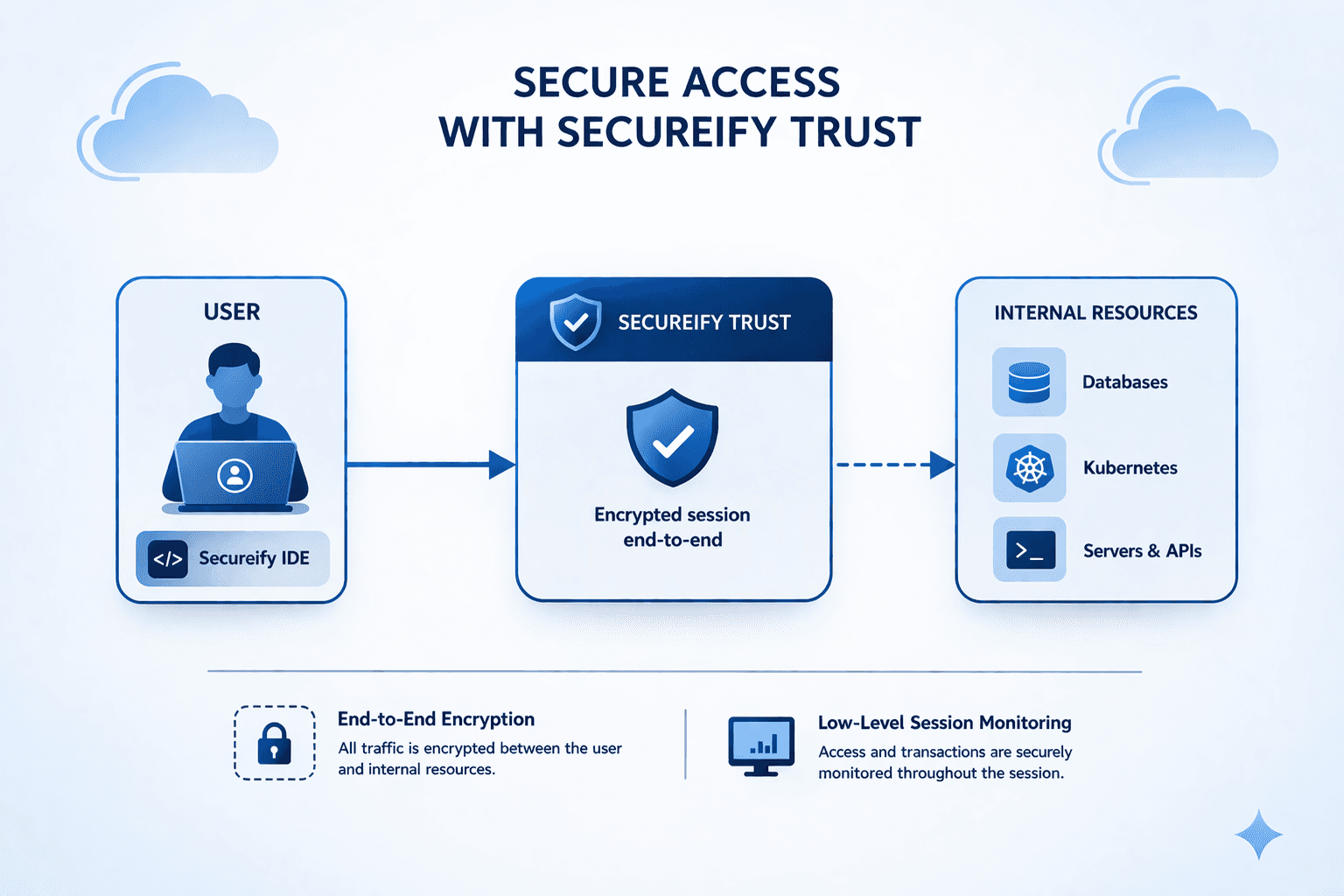
2. End-to-End Strong Encryption (By Design)
All communication is:
Fully encrypted in transit
Protected within secure memory
Never exposed to disk or external tools
Sessions are:
Bound to identity and device
Protected against replay and interception
Even if traffic is captured - it is unusable
3. Context-Aware Access Decisions
Every access request is evaluated based on:
Identity
Device posture
Location
Behavior
Trust score
And critically:
Trust is continuously verified in access runtime - not assumed
4. Desktop-Based Secure Access (Multi-IDE Experience)
Secureify Trust introduces a powerful concept:
Security integrated directly into the user’s working environment
The Secureify Desktop App:
Acts as a secure access layer
Integrates with tools Software Developers, DevOps and IT already use
Provides controlled access to:
Databases ( SQL - NoSQL ) IDEs
Kubernetes / Openshift IDEs
SSH
Web applications
This creates a multi-IDE experience, where:
Users work with familiar tools
Access is transparently secured
No credentials are ever exposed
5. Self-Hosted by Design (Privacy & Control)
Secureify Trust is fully self-hosted:
No external control plane
No third-party data routing
Full ownership of:
Identity
Access logs
Policies
Sessions
This aligns directly with:
Regulatory requirements in KSA and UAE
Data sovereignty principles
Enterprise privacy expectations
6. Unified Security Model
Secureify Trust consolidates:
Zero Trust Access
Identity & Authorization
Device Trust
Session Security
End-to-End Audit & Compliance
One platform - not fragmented tools
Why This Matters
Cybersecurity is shifting:
From credential protection → to credential elimination
From static access → to continuous and dynamic trust
From tool-based security → to architecture-based security
Organizations that continue relying on:
PAM
Vaults
Token-based access
Are not removing risk - they are managing it
Conclusion: The End of Credentials
The future of access security is not better password policies, faster rotation and more monitoring, It is:
A world where credentials no longer exist or the first factor of access decision
Secureify Trust delivers that future:
No credentials
Strong encryption end-to-end
Context-aware access
Fully self-hosted
Seamless user experience through a secure Desktop and multi-built in IDEs